The Digital Breadcrumbs You Leave Every Day — And How They Turn into Scams
Date
12 March 2026
Category
Secure Mojo Insights
Category
Personal Cyber Protection
Author
Chinmayi B S
Nothing suspicious. Nothing dramatic.
Just a small action you didn’t question.
That’s all it takes.
And the damage begins to spread quietly.
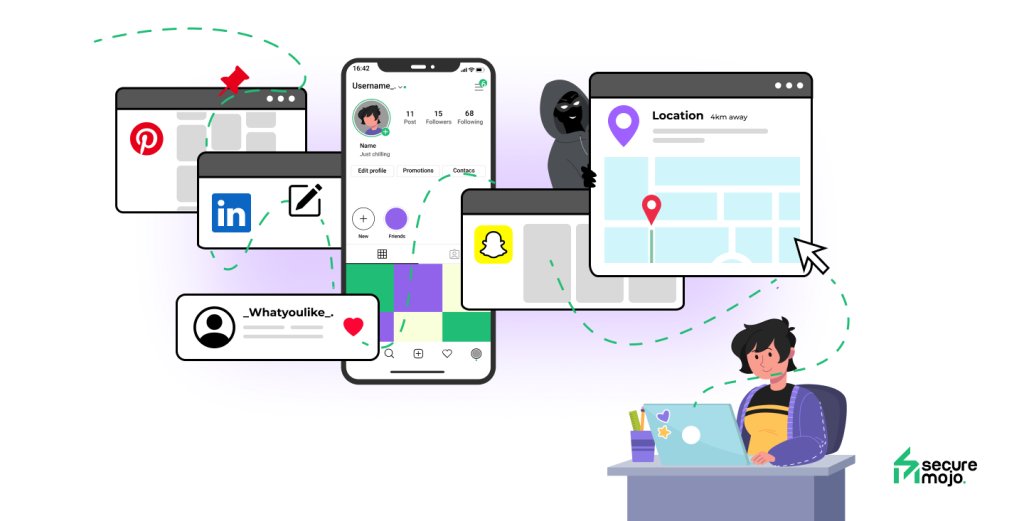
Every day, without realizing it, we leave behind small pieces of information online. A comment here. A post there. A profile update. A quick signup. Individually, none of these actions feel risky. They’re part of normal digital life.
But taken together, these tiny traces form a surprisingly detailed picture — one that cybercriminals know exactly how to exploit.
Most scams today don’t start with hacking tools or technical tricks. They start with observation. Attackers don’t break into your life; they quietly study it.
What Digital Breadcrumbs Really Are
Digital breadcrumbs are the bits of information you scatter online through everyday activity. Your job title on LinkedIn. Your birthday on Facebook. The apps you use. The brands you follow. The places you check into. Even the tone of how you write.
None of this is secret. That’s what makes it powerful.
Attackers don’t need confidential data when public information already tells them who you are, what you care about, and how you’re likely to respond. Over time, these breadcrumbs reveal patterns — your routines, your interests, your professional role, and even your level of authority or access.
To a scammer, this isn’t noise. It’s context.
How Normal Sharing Becomes a Targeting Tool
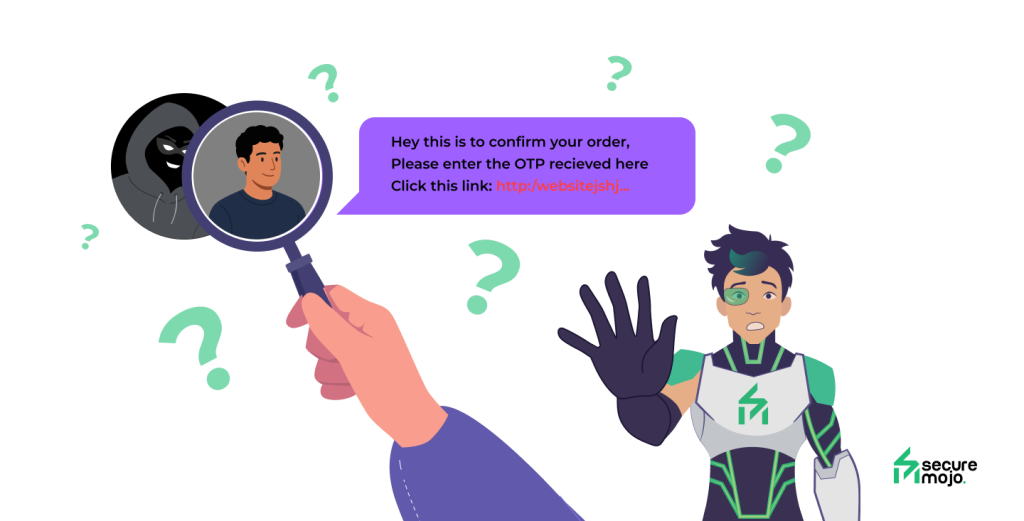
Most people assume scams are generic and random. In reality, many are highly personalized.
A post about starting a new job can trigger fake HR emails. Sharing travel plans can invite phishing messages disguised as airline alerts. Posting about a delivery delay can lead to a “follow-up” message that looks perfectly timed.
Attackers use public information to choose the right moment and the right story. When a message aligns with something already happening in your life, skepticism drops. The scam doesn’t feel intrusive — it feels relevant.
That relevance is what turns curiosity into clicks.

Why These Scams Feel So Convincing
Scams work best when they don’t feel like scams.
Messages are written in familiar language. They reference real tools, real companies, and real situations. Sometimes they even mention details you’ve shared publicly — your role, your industry, or a recent milestone.
At that point, the brain stops asking, “Is this safe?” and starts thinking, “This makes sense.”
This isn’t about intelligence. Smart, cautious people fall for these attacks because the message fits seamlessly into their reality. The attacker isn’t guessing — they’re responding to information already available.
When Breadcrumbs Lead to Bigger Damage
The danger isn’t just a single click. It’s what happens next.
Once attackers get a foothold, they often move laterally. Access to one account can lead to others. A compromised email can enable password resets. A hijacked social account can be used to scam friends, colleagues, or clients.
What began as harmless public sharing can escalate into identity misuse, financial fraud, or reputational damage — all without any dramatic “hack” ever taking place.
The trail of breadcrumbs simply led the attacker to the door.
Why Most People Never See It Coming
One of the most unsettling aspects of breadcrumb-based scams is how invisible they are. Victims often blame themselves after the fact, even though the setup was deliberate and calculated.
The attacker didn’t rely on luck. They relied on patience.
By the time something feels wrong, the interaction has already passed multiple internal “trust checks.” The message looked right. The timing felt right. The request seemed reasonable.
That’s why awareness matters more than fear. These scams don’t announce themselves — they blend in.
Reducing Your Digital Footprint Without Disappearing
Avoiding scams doesn’t mean going silent online or disconnecting completely. It means being intentional.
Small adjustments make a big difference: limiting how much personal detail is public, being cautious about what milestones you share in real time, and pausing before responding to messages that reference personal context or urgency.
When something feels too perfectly timed, that’s often the signal to slow down and verify through another channel.
You don’t need to erase your breadcrumbs — just stop leaving a perfectly mapped trail.
Final Thought: Context Is the New Currency
Cybercriminals no longer need stolen databases to run effective scams. Context does the job just fine. Everyday digital behavior — when unexamined — provides attackers with timing, credibility, and narrative. But the moment we become aware of how that information is used, the advantage shifts. Scams thrive on familiarity and speed. Awareness introduces friction — and friction is what stops most attacks.
You don’t need to be invisible online. You just need to be intentional.