Date
10 March 2026
Category
Secure Mojo Insights
Category
Personal Cyber Protection
Author
Chinmayi B S
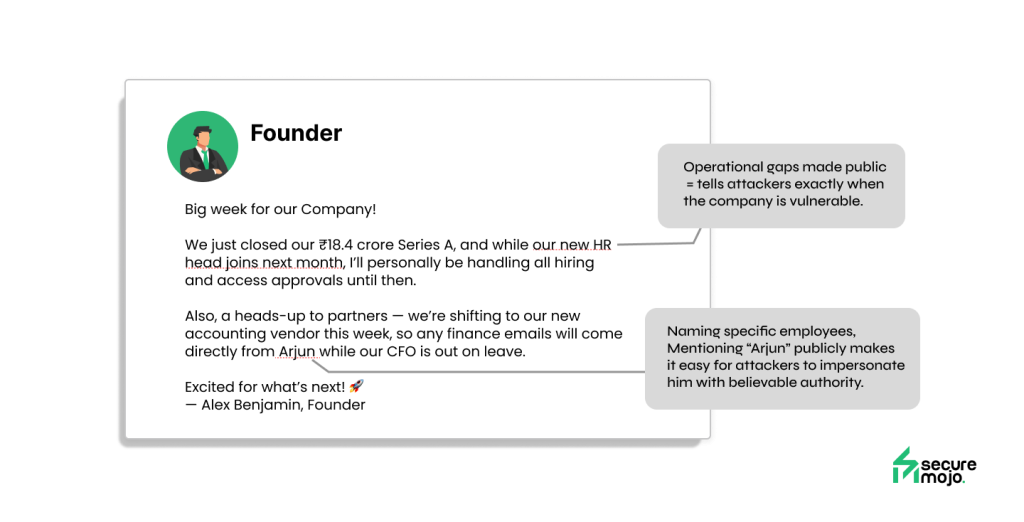
Founders build their presence on LinkedIn and similar platforms to signal growth, attract talent, and gain investor confidence. Public visibility becomes proof of momentum — and often a key part of the fundraising and hiring strategy. But that same visibility is increasingly becoming a blueprint for attackers.

Every update founders share online reveals small but important details about how their company operates — who handles money, who approves decisions, which tools the team relies on, and when things are hectic or high-stakes inside the business. It can also show who has access to important systems but may not be deeply trained in security.
Attackers don’t need to hack through systems when they can use this information instead. They take advantage of the trust founders build publicly and use it to create believable scenarios — pretending to be investors, recruiters, new partners, or someone asking for a quick favor that seems completely normal.
Social engineering has evolved from crude scams into context-aware impersonation built on real-time public intelligence. It looks like standard networking. It feels like legitimate business. And that is why it works.
What follows are real incidents publicly shared by founders, showing how normal professional interactions can rapidly turn into near-compromise or full identity hijack — without any technical breach at all.
This report shows how ordinary founder visibility online is now directly enabling targeted attacks — turning everyday networking into a serious security risk.
Stories That Hit Close to Home
Dejan Horvat posted:
“I almost got hacked today — twice.”
What unfolded wasn’t a clumsy phishing e-mail from a random spammer — it was business as usual: connection → calendar invite → a “Zoom link” for a meeting. On the surface, everything looked legitimate — mutual contacts, correct industry context, familiar workflow.
But the Zoom link redirected to a fake domain. A prompt asked to download a small executable (an “audio-permission fix”). That file was malware. One click, and Dejan’s system, credentials, corporate access — everything — could’ve been compromised. He caught it just in time. View Post
Pramendra Yadav experienced something even more insidious: a full account takeover. Overnight, his profile was hijacked. Same name. Same history. Same network. Suddenly, his identity became a vehicle for scams — fake messages, phishing attempts, maybe fraudulent outreach — all sent under his name. View Post
In that moment, not just Pramendra — everyone connected with him became vulnerable: co-founders, investors, vendors, anyone who trusted the profile.
Then there’s Vinayak Dhemare — who shared publicly that his account was taken over by attackers. Someone got control of his profile and began acting as him. Suddenly, a trusted founder identity became a tool for scams — fake outreach, suspicious messages, or harmful links sent to his own network. When a real account is hijacked, people don’t question it. They trust the name and respond normally. That’s what makes this so dangerous: the attacker doesn’t need to trick anyone — the founder’s reputation does the work for them. View Post
Mayank Goel – Founder of Growzzy Media faced a more destructive outcome. He received a business inquiry from someone posing as an HR representative at Chevrolet — complete with a polished email and campaign brief. When he opened the attached PDF, unfamiliar applications began installing on his system. Within moments, his LinkedIn profile was hijacked, his feed wiped clean, and nearly a year of content permanently lost. Even after multiple attempts to secure the account, the intruder retained deeper access than platform support initially detected. The attacker then used his profile to execute the same scam on others, endangering his brand and credibility. View Post
A robotics entrepreneur, Rushikesh Bagul , recently fell victim to a targeted phishing attack that resulted in the complete loss of his LinkedIn account and personal content history. Attackers locked him out, deleted his posts, and removed years of documentation — including robotics projects he had proudly shared, startup milestones, and professional updates. Although platform support eventually helped restore his access, the deleted content could not be recovered. Connections remained, but the digital narrative he had built to establish credibility in the robotics and startup ecosystem was erased. The attacker also used his account to send malicious messages to his network, forcing him to issue a public apology and reminder for others to stay vigilant. The incident left him rebuilding his professional identity from scratch — proof that a founder’s digital presence is fragile and can be wiped out faster than it was created. View Post
Another founder, Jagadish Ram Need it international, also reported a takeover of his LinkedIn account. Attackers leveraged his digital identity to send deceptive messages to his contacts while blocking him out. After regaining access and enabling multi-factor authentication, he was forced to alert his network to ignore any suspicious communication — a necessary step, but one that cannot undo the damage already caused during the attacker’s control window. View Post
These aren’t fringe cases. They show a new kind of threat: trusted-identity scams, post-fundraise phishing, and hijacked founder profiles.
The Numbers Don’t Lie: Social Engineering Is Now the Core Threat
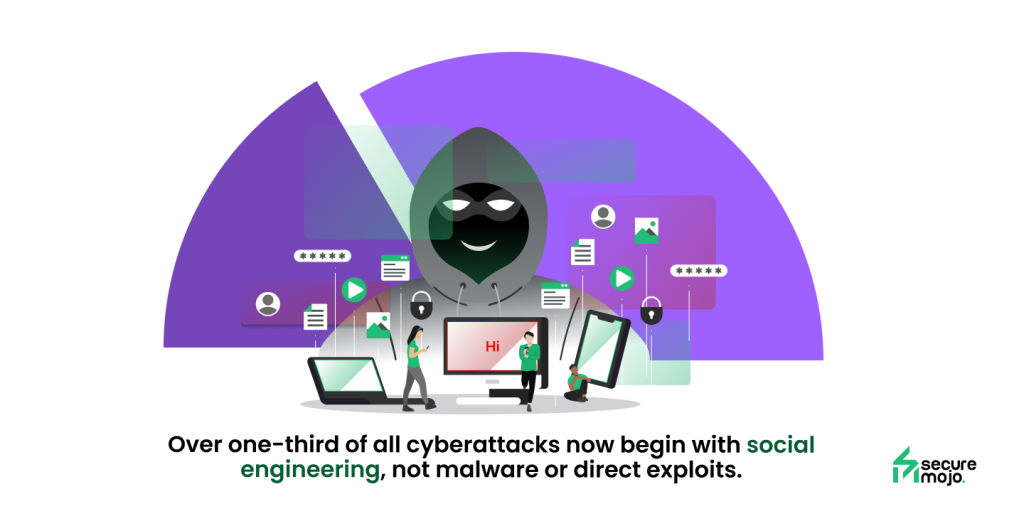
- Around 60–68% of all breaches in recent years involve human error or social engineering rather than some fancy exploit or bug.
- In 2024, global account takeover (ATO) fraud surged — reaching billions in damages.
- Over one-third of all cyberattacks now begin with social engineering (phishing, pretexting, fake links), not malware or direct exploits.
- For platforms like LinkedIn, social-media and professional-networking channels have become high-value for attackers. Recent reporting shows an alarming rise in account takeover and phishing campaigns via LinkedIn and similar networks.
- Even well-trained teams are vulnerable: in one 2025 study, many organizations found that human mistakes — not technical flaws — led to over half of successful incidents.
In short: social engineering — often initiated via platforms like LinkedIn — is now the default entry vector for attackers targeting startups and professionals.
Why This Matters — Especially for Founders
- Visibility = Recon-data: Every “We raised funding”, “Our new hire”, “Pivoting to X market” post leaks context: who manages money, who handles compliance, who handles payroll, hiring, operations. That’s gold for attackers building believable personas.
- Trust becomes the weapon: A compromised founder identity or just a “fake-but-real-looking” connection gets you right past basic skepticism. The workflow feels legitimate: messages, invites, meetings. That’s the whole point of modern social-engineering.
- The slip-up cost is high: One wrong click — a fake Zoom link, a downloaded “permission fix”, a doc share to the wrong person — and you expose internal data, finances, access keys, or even investor/vendor relationships.
For startups, that kind of breach isn’t just embarrassing. It can mean: client trust lost, deals gone, funds diverted, or worse — your entire company at risk.
What Founders (and Their Teams) Need to Start Doing — Immediately
You don’t have to go off the grid. But you need to start treating your public presence as part of your security surface:
- Inspect connection requests carefully — especially from people flooding in after a big announcement or raise. Treat them like someone walking into your office unannounced.
- Before accepting meeting invites or clicking links: verify domains, check email origins, and don’t assume a “Zoom link” is real just because the UI looks correct.
- Use strong security defaults — unique passwords, two-factor authentication (2FA), alerts for unknown logins or profile-change events (when the platform supports it).
- Limit what you share publicly about funding, team structure, timelines — especially financials, hires, and internal roles.
- Make verification a habit: if a “recruiter / investor / partner” contacts you — verify via external channels (official websites, mutual contacts, or direct calls) before granting access or sharing documents.
- Spread awareness within your team: founders, co-founders, ops, finance, recruiters — everybody should treat unusual requests as potential red flags.
Final Word
For founders, social presence isn’t just marketing or networking anymore. It’s part of your security perimeter.
- Your next connection request — or job-offer DM — could be a reconnaissance attempt.
- Your next “Let’s meet” invite could be a trap.
- Your own identity could be weaponized — silently, slowly, and with precision.
If you want to grow publicly — great, Just don’t forget: visibility ≠ safety.
Founder Takeaway
There’s a simple realization that emerges from these incidents:
The exposure isn’t only in systems or tools — it’s in the founder’s public identity.
Fundraising, hiring, partnerships — they all depend on staying visible.
But this same public activity gives attackers the perfect combination of timing, trust, and background details to launch believable scams.
Founders are always moving fast, assuming most outreach is genuine, and sharing their journey openly online. Attackers need only one of those factors to successfully take advantage of that openness.
The mindset shift that follows:
Staying visible is essential.
Because once a founder becomes part of the company’s security surface, safeguarding that identity stops being optional — and becomes a core part of risk management.